We are all too familiar with the problems of passwords. New data from Microsoft provides a unique perspective on the state of cybersecurity based on 43 trillion signals from billions of logins every day. The 2022 Microsoft Digital Defense Report reveals:
- The volume of password attacks has risen to roughly 921 attacks every second.
- Password attacks increased 74 percent in the past year.
- Roughly 20 percent of people reuse the same passwords for many websites and apps, making them easy targets for credential stuffing or password spraying.
- Over 90 percent of accounts compromised by password attacks lack strong multifactor authentication (MFA), like SMS OTPs or FIDO2 authentication.
The report goes on to say, “We have seen a rise in targeted password spray attacks, with very large spikes in the volume of attacker traffic spread across thousands of IP addresses.” The attackers’ efforts to hide from standard defenses and remain untraceable highlight yet another problem. Threats are growing more sophisticated.
Why replace passwords and basic MFA?
MFA has become essential to fend off the growing volume of digital identity threats and prevent account takeover (ATO) fraud. But for many organizations, SMS one-time passcodes (OTPs), magic links, and authenticator apps add more friction than their customers will tolerate.
More importantly, these multi-step MFA methods are still vulnerable to smishing, man-in-the-middle, and other attacks, resulting in a clunky customer experience that is susceptible to compromise.
PSD2 compliance: Is your MFA strong and simple enough?
To comply with security regulations like PSD2’s strong customer authentication (SCA), most financial services use SMS OTPs or an authenticator app. But the added friction of having to download and use an app reduces the customer adoption rate, and OTPs can lead frustrated customers to call support or drop off entirely.
The combination of an OTP and a password technically meets the requirement for two factors, but this won’t prevent ATO fraud if the device is infected with spyware or the session is hijacked. To take over accounts at scale, hackers are now using OTP interception bots that make it easier than ever to snag passcodes in transit. Plus, some bad bots bypass OTP authentication altogether.
How passwordless MFA works differently
When you authenticate customers based on FIDO2, the most current set of passwordless standards by the FIDO Alliance, you know who is accessing the account. And, if done correctly, you completely eliminate shared secrets — not just passwords but OTPs and all data that could expose you to attacks.
With true passwordless authentication, customers simply use a fingerprint or facial biometric to achieve the strongest form of MFA in one simple user action. Logging in is faster, easier, and vastly more secure.
How is it multifactor? Only the real customer’s biometric (inherence factor) unlocks a private key (possession factor) stored on the user’s device.
What’s to prevent the biometric and private key from being compromised? By leveraging public key cryptography (PKI), the biometric and the private key remain secure, never leaving the user’s device. The private key signs the authentication challenge, and only the signed challenge, void of any identifying data, is sent over the web. On the receiving end, the matching public key is used to verify the challenge. It all happens in a few seconds, and you’ll know who the individual is with a high level of confidence.
Key differentiators to look for in a passwordless solution:
- MFA by design: Methods should include FIDO-based passwordless and passkeys.
- With your mobile app or web app: Gain flexibility to optimize customer experience and security as needed.
- Omnichannel experiences: Let users move across channels with a single identity.
- Multi-device support: Enable users to log in from any of their devices.
- Ease of deployment: Plug-and-play services optimize all scenarios and flows.
- Continually updated for compliance: Stay in compliance with a service that’s continually updated to meet the latest requirements.
Integrate Transmit Security passwordless MFA with Azure AD B2C
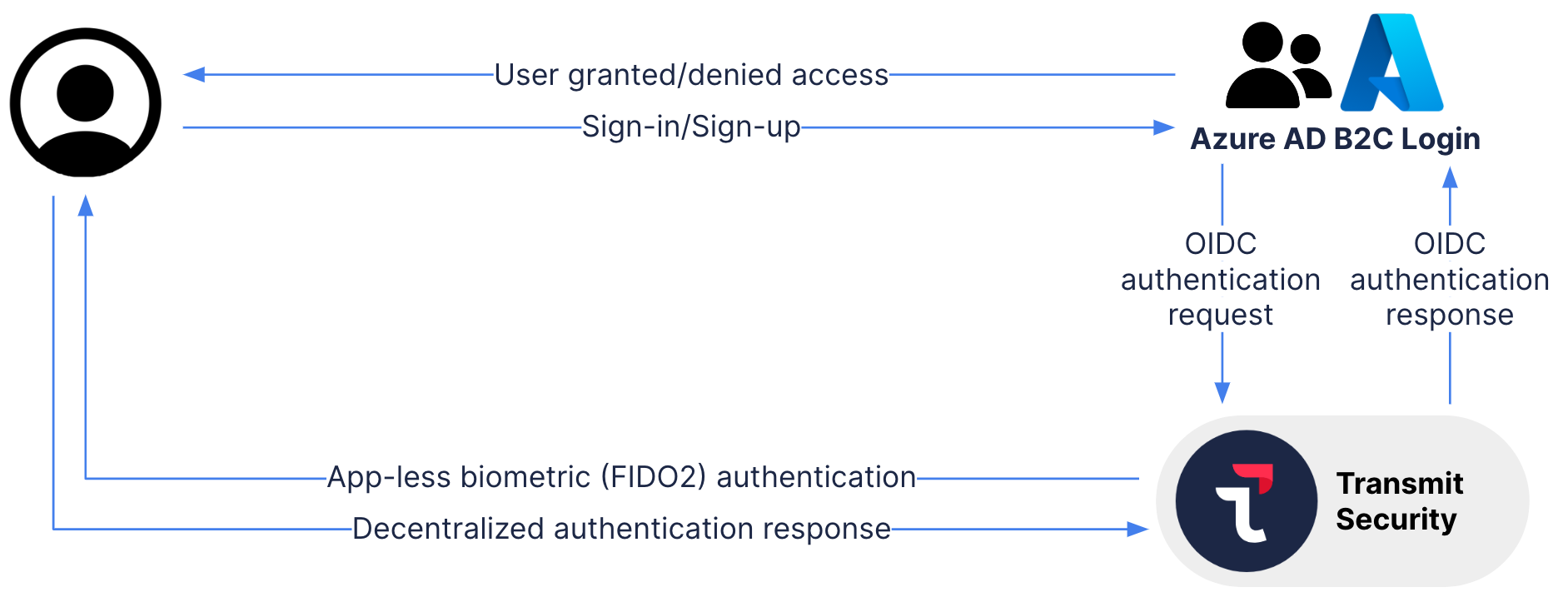
You can now fortify Microsoft Azure Active Directory B2C with Transmit Security passwordless MFA (available in the Azure Marketplace), designed to authenticate customers based on their true identities.
With Transmit Security, customers only register one account with your business and then log in with a biometric on any channel, using any of their devices, without ever entering a password or storing credentials in the cloud. Our unique device-binding method makes it easy and secure for customers to transfer trust to any of their devices, binding them all to one unified identity.
This cloud-native service seamlessly integrates within your new or existing Azure implementation. Passwordless MFA works alongside all methods of authentication provided by Azure AD B2C and supports other implementations like FIDO passkeys, an extended version of FIDO credentials. This allows you to give customers login options that satisfy their preferences while enhancing your security posture. Over time, you’ll be able to transition all customers to passwordless.
In a press release announcing support for the FIDO standard, Alex Simons, Corporate Vice President, Identity Program Management at Microsoft, said, “The complete shift to a passwordless world will begin with consumers making it a natural part of their lives. Any viable solution must be safer, easier, and faster than the passwords and legacy multifactor authentication methods used today.”
“Microsoft is thrilled to have Transmit Security as a Solutions Partner for Security,” said Yvonne Muench, Senior Director - Marketplace & ISV Journey at Microsoft. “Transmit Security is committed to helping Microsoft customers leverage the benefits of passwordless authentication via Microsoft Azure Active Directory B2C. Having an experienced and trusted security partner like Transmit Security building on and augmenting native Azure capabilities really helps support and drive the vision of a passwordless future.”
Visit Microsoft Learn for a simple step-by-step guide on how to configure Transmit Security passwordless MFA with Azure AD B2C. You can customize or brand the UI and roll out hundreds of user flows out of the box. It’s easy to set up secure and smooth password-free experiences across all channels and devices.
Secure the full identity lifecycle
By removing customer passwords, your greatest security risk is gone. But today’s more sophisticated ATO fraud can compromise customer accounts before, during, and after the login. By implementing passwordless MFA as well the Transmit Security Risk, Trust, Fraud, Bots & Behavior Detection service, you’ll seal the cracks across the full identity lifecycle.
Real-time risk and trust assessments correlate hundreds of signals to detect signs of ATO fraud anywhere in the customer journey, from registration to account recovery and every step in between. Any time risk is detected, you can challenge the user with true passwordless MFA. Together with Azure AD B2C, you’ll gain a formidable defense against ATO fraud.
Explore what you can do with Azure AD B2C and Transmit Security. Or better yet, get the ball rolling — see our technical brief on how to integrate passwordless MFA in 4 simple steps.



