Fast identity online (FIDO2) isn’t just about improving your own cybersecurity efforts. It’s a calculated approach that also improves your users’ experiences and reduces friction while navigating their online accounts with you — whether those users are your employees or your end customers.
In this article, we’ll cover three core reasons why adopting FIDO2 protocols in your authentication processes can positively impact your user experience, customer loyalty and revenue — giving your company a strong competitive advantage.
Password sharing is still common practice
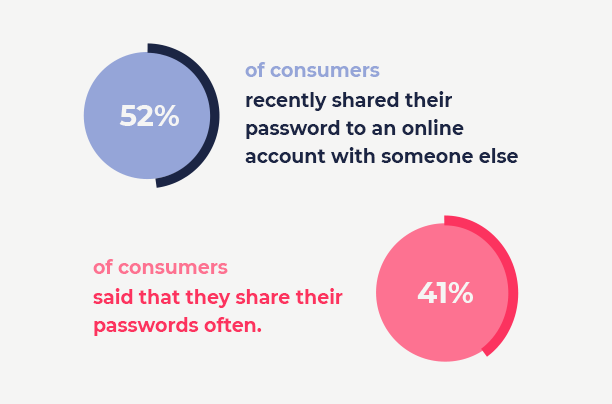
In a recent survey we conducted, 52% of consumers said that they have recently shared their password to an online account with someone else. And 41% of consumers said that they share their passwords often. These statistics show that customers are seemingly not bothered by the deeper implications of sharing passwords with their friends, partners, or work colleagues.
When users share their passwords with others it impacts business in the following ways:
Licensing abuse: If users have access to a password for an already paid account they are effectively avoiding paying (which means less revenue for you as a service provider) for a second account. Users of services like Netflix or MasterClass, which offer on demand viewing, share passwords freely knowing their experience will be somewhat jeopardized in order to avoid additional payment.
Usage monitoring and personalization: If accounts are being shared by multiple users, service providers are less likely to accurately monitor usage and are unable to correctly personalize their offerings – their user experience can’t be optimized or personalized to meet their users expectations. Service providers can’t give their customers what they want because they are unable to see clear user activity. This inability directly impacts potential revenue. With incorrect data, effective targeting becomes impossible as there is no clear picture of who the actual account holder is. Questions like, what do they like? When are they active? And how can you upsell them all become hidden mysteries. The loss of potential revenue here is enormous (and unfortunate).
Security: Given that 65% of users re-use the same password across multiple accounts (Google) once users share that one password with someone else they are essentially handing over access to multiple accounts they own. Hackers know (and use) this too which is why they are able to successfully hack into multiple accounts of the same user.
FIDO2 solves these critical business issues by eliminating the need for passwords. Users are authenticated using strong built-in, device-based biometrics through a device belonging to the user. Resulting in authentication processes that are:
- Simple, secure and frictionless for users.
- Ensures that every account has only one intended user.
- Enables strategic account personalization and targeted ads to increase customer loyalty and revenue.
Simple, seamless and frictionless user authentication experiences

Today’s users expect their online experiences to be totally seamless. From account creation to logging in to checkout. But in some cases, there’s still a fine line that divides smooth user experiences from safe and secure ones.
And this is exactly where FIDO2 comes in. Instead of using multiple tools to serve multiple layers of authentication for users, FIDO2 serves users strong biometric authentication using a single tool or smart device — whether that’s via a mobile phone, PC, laptop or tablet.
This significantly reduces users’ authentication time while reducing the need for passwords and reduces the friction in serving users multiple layers of authentication. Either way, it lifts an enormous burden off users’ shoulders, allowing them access to their accounts in seconds without copying codes, memorizing passwords, or using additional device or platform authenticators.
The secondary advantage of seamless user experiences is that they increase customer satisfaction and loyalty. Even though authentication processes are in place to protect their best interests as well as yours, customers don’t see it that way. So the more simple your authentication experiences are, the more your customers feel “seen” and respected by you. Which in turns, translates into greater engagement while reducing account and cart abandonment.
Undeniably secure with better resistance to hackers and phishing attacks
Adopting FIDO2 doesn’t just benefit your end users. The way FIDO2 is designed naturally increases companies’ cybersecurity efforts against hackers — and specifically, against phishing attacks, due to a built-in mechanism.
FIDO2’s strong biometrics eliminate the need for passwords and multiple, static layers of authentication via private (or public) key cryptography. Each device is assigned a unique, encrypted key relating to a specific account. And with no two account keys the same, this immediately reduces a company’s vulnerability to hackers and phishing attacks. And because this eliminates the need for passwords altogether, there’s absolutely nothing left for hackers to steal — which ensures your company’s and your users’ data stays safe and secure at all times.
Implement effortlessly with Transmit Security
Another advantage of adopting FIDO2 protocols is that it makes it easier for companies to deploy — and update — their cybersecurity efforts at scale. Unlike legacy cybersecurity software that needs to be woven into the end-code of every web app, FIDO2 authenticators are available in almost every platform (Android, iOS, and Windows), and across every web browser (Chrome, Safari, Firefox, and Internet Explorer), so launching FIDO2 can be done more swiftly than legacy alternatives.
But while FIDO2 provides a solid foundation for implementing strong authentication, companies will still need some help deploying it successfully. Aside from implementing the new authentication protocol, which includes generating WebAuthn requests and running the cryptographic verification process on the response, an authentication interaction model or a third party service can help make the transition much smoother. Transmit Security delivers the industry’s first app-less, strong portable authenticator that uses device-based biometrics for secure, convenient and consistent customer authentication. Applications handoff the complexity of maintaining real-world FIDO2 authentication scenarios to the service, which takes care of all authentication flow details and gets back to the application with a final detailed and secure authentication result. Meaning you can implement effortlessly and verify instantly.
Ready to implement the latest authentication technology? Discover more here!



